Understand Token Behaviour
Manage Risk In Real Time
Characterize token behavior, assess risk, and monitor on-chain activity across all EVM networks.
Contact Sales
How Token Custody Works
Simulate real-world EVM execution across multiple contracts.
Test transactions, upgrades, and edge cases to proactively identify custody risks and exploitable vulnerabilities.
.png)
AI classifies results into clean, precise behavior primitives.
Contracts are continuously re-tested to catch changes and new behaviors
Combines behavior simulations and risk signals to forecast malicious collapses
Token Custody Features
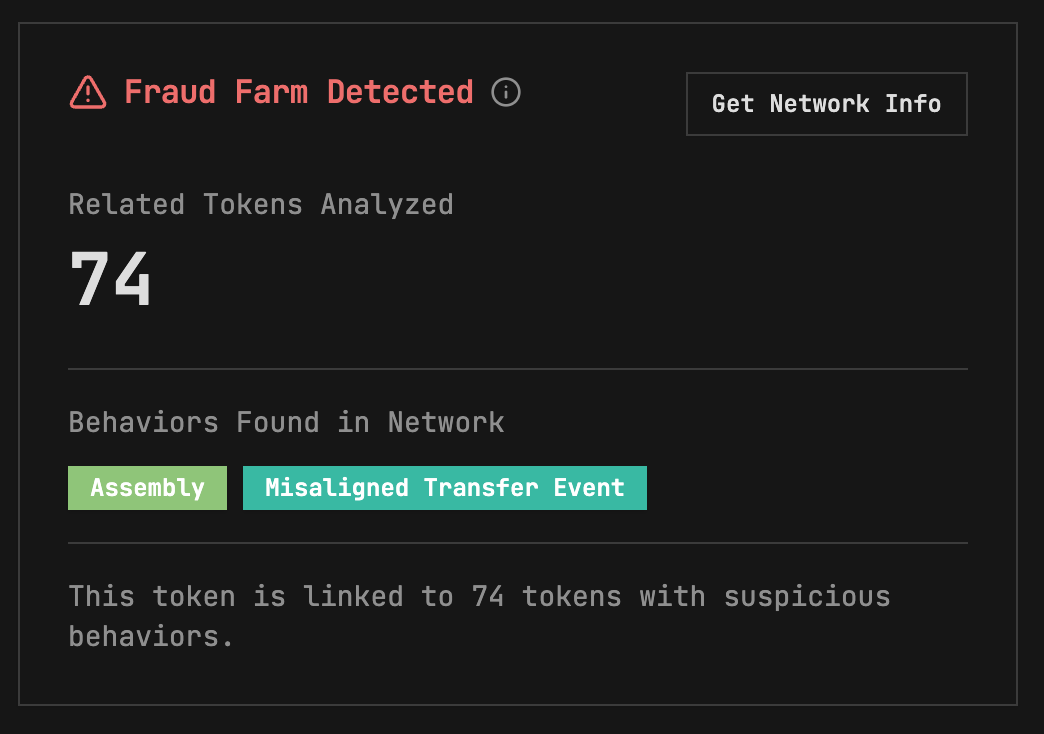
Fraud Farm Detection
Expose token reputation before you list or buy
Identify whether a token is connected, directly or indirectly, to networks of past fraud
Detect repeat scam operators across multiple deployments.
Uncover hidden links through funding paths and token lineage.
Assess risk in context, not in isolation.
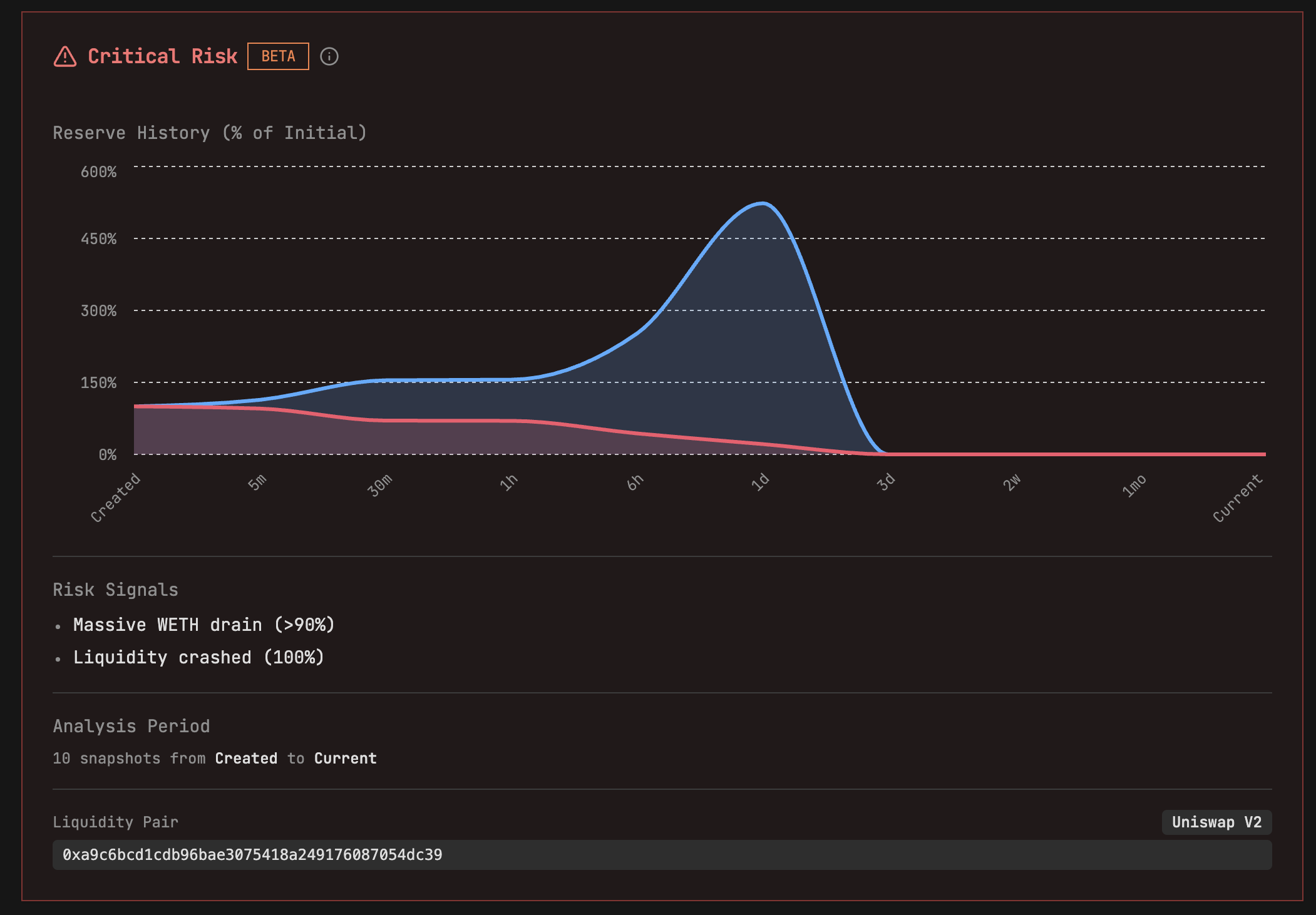
Rug Pull Risk Analysis
Detect liquidity drain before it destroys value
Rug Pull Risk Analysis monitors on-chain liquidity to detect when value is extracted from a token’s trading pools, the primary driver behind rug pulls.
By tracking native asset withdrawals from liquidity pools, it flags high-risk behavior with precision, even as attack methods evolve.
Outcome-focused, not signature-based.
Detects liquidity drains regardless of technique.
Minimizes false positives while surfacing real risk.

Token Risk score
Clear risk signals at a glance
Token Custody assigns every asset a dynamic risk score giving you an immediate, comparable view of risk before listing, buying, or monitoring.
Scores reflect real on-chain behavior, not static labels or surface-level heuristics.
Instantly assess token risk.
Compare assets side by side.
Monitor how risk evolves over time.
$120M
7 Million
100%
Prevented in rug pulls so far
Tokens continously monitored
Of rug pulls identified in an analysis of 11,000 tokens
Chains Protected by TestMachine
All EVM Chains Covered

.png)


.png)
.png)

.png)


.png)
.png)

.png)


.png)
.png)
.png)