Waiting for next protocol…
Researching potential targets...
LiveAzimuth Attack Agent
LiveWe build security infrastructure for the agentic age… and it works
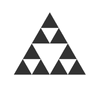
75.2% Detection Rate on EVMBench
~2.7% Observed False Positive Rate
~$100 Average user cost per EVMBench repo
Frontier model with vanilla coding harness
Frontier model with vanilla coding harness with Pashov skill
TestMachine Azimuth
Number of vulnerabilities identified in an EVMBench audit
See Azimuth's full EVMBench results on our leaderboard
Backed by the Best in the Business
Get in Touch
Ready to secure your Web3 project? Let's talk about how TestMachine can protect your protocol.
We typically respond within 24 hours.
Or email us directly at contact@testmachine.ai
20 W 34th St, New York, NY